Blog
6 Cyber Attack Prevention Tips for Small Businesses (with 5 Common Cyberattack Examples)
Cyber attack prevention for small business doesn’t have to be complex—start with these 6 simple defenses to stay secure.
What new ransomware trends mean for your security strategy
Ransomware trends in 2024 reached record highs. Discover the latest attack methods, security gaps, and five steps to protect your business.
Protecting Your Business from the Growing Threat of Deepfake Technology
Fake voices, videos, and misinformation are the new tools of cybercrime. Explore the risks of deepfake technology and actionable ways to stay safe.
How Zero-Day Exploits Are Becoming More Common and How to Prepare
Zero-day exploits are targeting your vulnerabilities before you know they exist—here’s how to fight back with smarter defenses.
Why Microsoft Sentinel Is the Next Big Thing in Threat Detection
Explore the benefits of Microsoft Sentinel for real-time threat detection, seamless integration, and proactive security.
The Dangers of Session Theft and AiTM Attacks
Discover how to defend your organization from AiTM attacks and session theft with strategies that secure your data and strengthen trust.
Microsoft September 2024 Updates
Explore new Microsoft updates boosting security and streamlining workflows with features like location-based presence and stronger passcodes.
Choose the Right MFA Method for Your Security [An In-Depth Comparison]
Explore the strengths and weaknesses of three different MFA methods to help you choose the best option for your protection.
How Businesses Can Respond to Incidents Like the Avis Data Breach
See how businesses can manage data breaches, like this Avis incident that exposed customer information, and protect their systems from future threats.
Protect Yourself from Scams During Hurricane Milton
As Hurricane Milton makes its way through the Gulf Coast, it’s important to stay alert to scams that arise in the wake of natural disasters.
Enhancing Data Protection with CoPilot for M365: A Comparison of RSS and SAM Controls
Explore the data protection controls available through RSS and SAM and get a comprehensive comparison of their features with CoPilot for M365
What You Should Know About Microsoft’s New AI-Powered Security Tools
Microsoft has made significant progress infusing AI into their existing security tools to make businesses more secure.
How to Stay Compliant with New US Cybersecurity Regulations Using Microsoft 365
Microsoft 365 offers a comprehensive suite of tools and services designed to help businesses meet these stringent requirements.
All You Need to Know About the CrowdStrike Incident (Tips to Recover Fast If You’re Affected)
The recent CrowdStrike update issue impacted Microsoft users, causing recovery challenges and a surge in phishing scams. Find recovery steps and tips to strengthen your cybersecurity strategy.
Spot These Scam Error Alerts [+5 Tips to Stay Safe]
Scam alerts in Google Chrome and Microsoft Word are rising. These scams can cause serious security breaches. See to identify and avoid them.
5 Key Lessons from the Ascension Ransomware Attack
Review the critical lessons learned from the Ascension ransomware attack and implement them to safeguard your organization.
What Microsoft Defender XDR’s Achievement Means for Your Protection
Discover how GCS Technologies leverages Microsoft Defender XDR, a leader in the Forrester Wave™, to enhance your business’s security.
Keep New Hires Safe from Cyber Threats
Cyber threats are becoming increasingly sophisticated, targeting even the most unsuspecting individuals. From day one, it is crucial to protect employees and ensure they are equipped to recognize and respond to potential threats.
The Security Gap Behind the Change Healthcare Attack
A recent cyberattack on Change Healthcare, which significantly disrupted healthcare systems nationwide, was attributed to a lack of multifactor authentication (MFA) on a key server.
Black Basta Ransomware Exploits Windows Quick Assist for Remote Attacks
Black Basta, a global ransomware campaign, has been known to abuse Windows Quick Assist to gain control over targeted victim’s machines. Windows Quick Assist is a remote view/control application built right into Windows for use by technical professionals while...
RingCentral case study
When the TBA faced the urgent need to adapt to a rapidly changing work environment, they turned to GCS Technologies…
AI Deepfakes: How to Protect Your Business from The New Cyber Deception
AI deepfakes are the latest threat to your organization’s reputation, data, and finances. Discover security measures to minimize the risks.
Is Microsoft Copilot Safe to Use? 5 Questions to Assess Your AI Security Risk
Microsoft Copilot can boost your productivity – but at what cost to your security? Get 5 questions to assess your AI risk in this 5.5 min read.
What Is Cybersecurity Awareness Training and Why Does Your Team Need It?
What is cybersecurity awareness training? One of your best defenses against common cyber threats. See how it could protect your business in 5 minutes.
Ransomware Alert: The #1 Cyber Threat to Your Business Is Rising
Discover the rising threat of ransomware to businesses – learn how ransomware groups cost companies billions and how they operate.
Warning: Rise in ZeroFont Phishing Attacks on Microsoft Outlook Users
Threat actors have a new tactic in their toolbox — and it could put your data at risk. Here’s what you need to know about ZeroFont phishing.
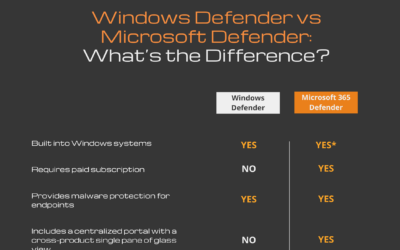
Windows Defender vs Microsoft Defender: What’s the Difference?
Discover the crucial distinctions between Windows Defender vs Microsoft Defender in the ever-expanding cyber-threat landscape.
The Risks and Mitigation Strategies for New Top-Level Domains
With the recent introduction of new top-level domains (TLDs) by Google, users now face potential risks that can lead to phishing attacks.
The Ultimate Guide to Microsoft Secure Score
Safeguard your organization from cyber threats by understanding and improving your security posture with Microsoft Secure Score.
Why Buying More Bandwidth Might Not Solve Your Office Internet Issues
Many businesses mistakenly think that they can solve their office internet issues by adding more bandwidth. However, office environments are far more complex than residential ones, and purchasing a bigger internet connection may not always be the solution. In this...
Large Ransomware Attack on Rackspace Hosted Exchange: Time to Move to Microsoft 365?
Rackspace is a U.S-based cloud computing service provider with customers in 120+ countries. On December 2nd 2022, many Rackspace customers began experiencing problems logging into and accessing their email accounts held in their Rackspace Hosted Microsoft Exchange...
What is MFA Bombing?
Multi-factor authentication (MFA) is a security technique that requires users to provide multiple forms of authentication when accessing a system or service. This means that in addition to a username and password, users must provide an additional piece of information,...
When Should You Switch IT Support Providers? Watch Out for these 3 Signs!
Every business requires some level of IT support providers to help manage cybersecurity, data backups, disaster recovery, cloud migration, and even help desk support. To maintain these services, there are two options: 1) create and maintain an in-house team 2) work...
What to do after your managed service provider has been acquired
Many of Austin's largest managed service providers have been acquired.… Client satisfaction and continuity are rarely a consideration in these liquidation events. Over the past several years, GCS competitors have been acquired at a brisk pace. The race to roll up IT...
Forrester Wave reports acknowledging Microsoft’s dedication to enhancing IT security network
Microsoft’s commitment to improving IT security network has recently earned its recognition as a leader in seven Forrester Wave reports








![Choose the Right MFA Method for Your Security [An In-Depth Comparison]](https://www.gcstechnologies.com/wp-content/uploads/2024/10/mfa-400x250.jpg)






![Spot These Scam Error Alerts [+5 Tips to Stay Safe]](https://www.gcstechnologies.com/wp-content/uploads/2024/06/shutterstock_2456842111-400x250.jpg)